Blog
Building TextFSM Templates: A Beginner’s Guide
Building TextFSM Templates: A Beginner's Guide TextFSM is a powerful tool for parsing the outputs of structured text, such as CLI outputs, into structured data formats. This guide provides step-by-step instructions on building TextFSM templates, enabling you to...
Use cases
Building TextFSM Templates: A Beginner’s Guide
Building TextFSM Templates: A Beginner's Guide TextFSM is a powerful tool for parsing the outputs of structured text, such as CLI outputs, into structured data formats. This...
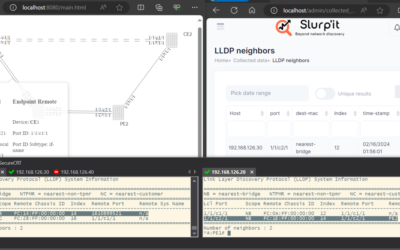
Complex Network Topology Discovery using Slurp’it
Guest post by Flavio Esquivel In this guest post, Flavio delves into the practical application of Slurp'it for network topology discovery. Through hands-on experimentation, he...
PoC Network Topology Discovery using Slurp’it
Guest post by Flavio Esquivel In this guest post, Flavio delves into the practical application of Slurp'it for network topology discovery. Through hands-on experimentation, he...
New NetBox-Slurp’it plugin to discover & onboard your network in no time
Tired of manually documenting your network devices and struggling with keeping your NetBox up-to-date with accurate information? The new Slurp'it plugin for NetBox seamlessly...
Supercharge Network Onboarding with Slurp’it and NetBox
UPDATE! Official Netbox Slurp'it plugin launched, read more here > Every Managed Service Provider (MSP) knows that taking on a new customer means navigating a complex...
How Slurp’it Uncovered a Hidden Network of Raspberry Pis at a Global Bank
A large bank discovered the capabilities of Slurp'it, in a rather unconventional yet enlightening security test. What started as a simple internal security audit quickly...
Blog posts
Regular Network Security Audits: Assessing and Improving Network Vulnerabilities
If you run a business, you can't stay away from cyber threats. And here's where network security comes into the picture, followed by auditing. This blog talks about what is...
Network Virtualization: Enhancing Flexibility and Efficiency
Virtualization - the concept has been around for years. LAN, overlay networks - we have heard of these a lot. But the transformation didn't stop here. The traditional network...
Building TextFSM Templates: A Beginner’s Guide
Building TextFSM Templates: A Beginner's Guide TextFSM is a powerful tool for parsing the outputs of structured text, such as CLI outputs, into structured data formats. This...
Decoding Anomalies: Enhancing Network Security through AI-driven Behavioral Analytics
Can artificial intelligence protect you from digital threats? Well, we have a lot to share. But let's get into the core first. Network security is important. Reason being, the...
Why and How to Implement Data encryption in small business networks ?
Small businesses are the targets of cyber threats. And this is not us telling this, but a statistic stating that the global cost of cybercrimes is about to jump to $33.84...
The Art of Mapping Networks: Strategies for Efficient Network Discovery
Efficient network discovery is something that has become much more critical these days. But this article will solve all your issues. In this piece, we will give you detailed...