Ransomware, advanced persistent threat, and so much more – there is a big list of cyberthreats a business faces these days. And because of this, growing in this competitive market gets difficult.
One has to effectively manage vulnerability. For this, the business has to be aware of everything that exists. This is where it plays the major role. Let’s understand in detail how!
Now,
Why does network discovery scans matter?
Let’s say you’re managing a big warehouse with multiples of boxes, probably in thousands, but you don’t really have any inventory list by your side. A big disappointment. In the case of network discovery scans, IT teams are blind to shadow IT devices. Also rogue endpoints or outdated systems that pose security risks. And here’s where things often go wrong.
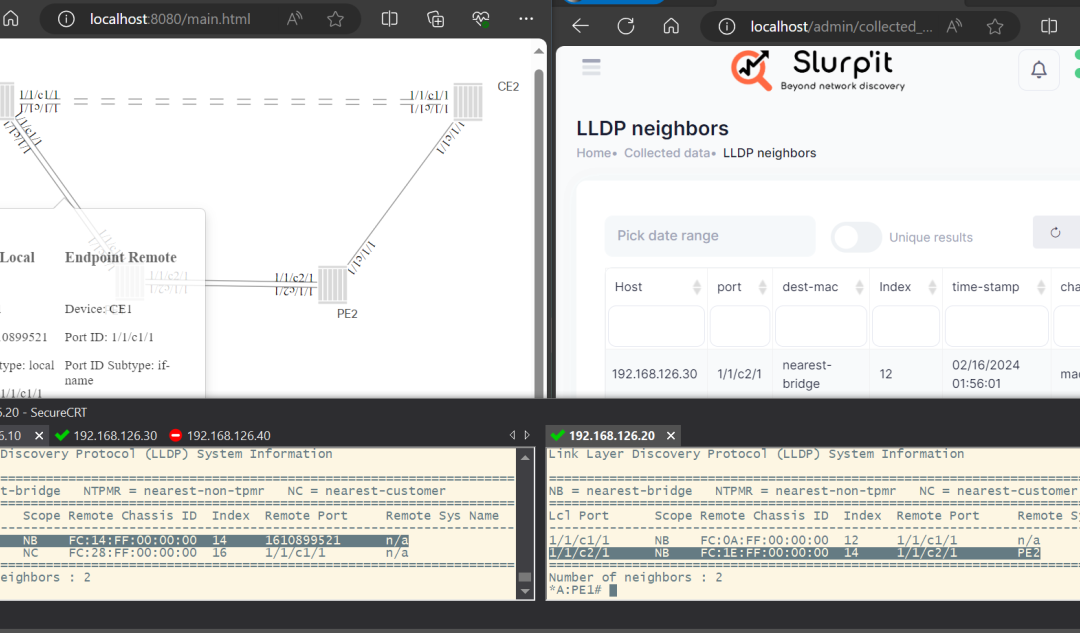
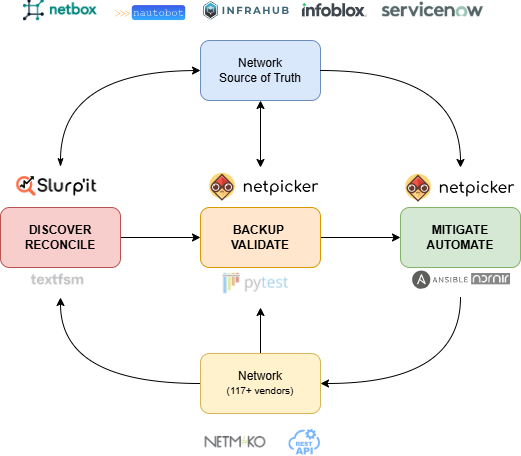
It actually identify every connected device. Also the service and application on a network. From forgotten printers to servers that go unpatched, these scans expose hidden issues. Hence IT teams, with this information can prioritize fixes based on real-time visibility that they have as per Slurp’it.
How can one prevent a security breach?
We would explain this with an example. There’s a mid-sized financial firm. They were preparing for a compliance audit. And a network discovery scan actually revealed outdated Windows XP machines. These were still connected to sensitive databases as per Slurp’it.
Without this scan, the company would have faced security risks and compliance penalties. But just a quick scan helped them with avoiding both financial and reputational damage as per Slurp’it.
How network discovery scans improve vulnerability management?
Now let’s come to the main part. How can network discovery scans actually help with network management:
- It gives businesses complete asset visibility. Each scan provides a full view of all connected devices. Businesses can quickly identify all the unpatched vulnerabilities, like any unauthorised IoT devices or outdated firmware.
- We know networks are massively dynamic in nature. New devices are added almost on a regular basis. But if the scannings are done continually, vulnerability management remains up to date.
- We understand that not all vulnerabilities are equal. It actually helps organizations focus on securing the most at risk assets based on both their exposure and role.
- Shadow IT devices, unauthorised systems are major security risks to most businesses. And it actually expose these devices quickly so that businesses can secure them as per Slurp’it.
Challenges that come with network discovery scans!
Network scans help best with vulnerability management. But it does come with a lot of challenges. Some specific ones include:
- Network performance impact. Running them on any live network can slow down performance. But one can mitigate this issue. Businesses can schedule scans during offpeak hours and use low-impact scanning methods.
- Regulatory frameworks like GDPR, HIPAA, and PCI-DSS require strict control over scanning processes. Organizations should make sure that all their scanning activities comply with laid industry standards.
- Enterprise-wide network discovery scans generate vast amounts of data. Hence businesses can think of integrating these scans with intelligent vulnerability management tools. This will actually help them analyze and prioritize findings quickly.
Some best practices for integrating network discovery scans
- Make sure to automate discovery and remediation
Try linking it with vulnerability management platforms. Because of this, newly detected assets are automatically assessed and secured without manual intervention.
- Schedule regular scans
The more frequent the scans are, the better the visibility gets. If the environment you work in is quite dynamic, daily or weekly scans are suggested. Whereas, monthly scans may suffice for stable networks.
- Combine both active and passive scanning
Active scans probe devices. On the other hand, passive scans monitor network traffic for silent threats. If a business uses both the methods for scanning, security checks get easier, even without overloading the network.
- Always maintain accurate asset inventories
Make sure to update all the results obtained through scanning in a centralized asset inventory. This helps IT teams track all connected devices.
- Try aligning scans with compliance requirements
All your scans should follow regulatory guidelines. Make sure to maintain proper documentation for audit purposes.
What is the future of network discovery and vulnerability management?
Now that you have understood why network discovery is really important for vulnerability management, last comes the main part, what’s the future of this thing. Hybrid cloud environments, remote working, IoT, they are becoming more critical than ever. Modern solutions are now using AI and machine learning to predict vulnerabilities and recommend fixes.
Looking ahead, future systems may not only detect devices but also predict which ones are most likely to be targeted using global threat intelligence. So, are you ready to secure your network? Start with network discovery scans now and manage all the vulnerabilities, the smarter way, with a proactive defense system! For more information contact us at Slurp’it.